It all started on 9/11/2001. Two hijacked planes bring down New York’s World Trade Centre, and a third crashes into the Pentagon. The fourth plane dives into the ground as mutinous passengers confront the hijackers. A wounded empire responds instantly; the bombing and invasion of Afghanistan is followed by the bombing and invasion of Iraq. The world’s media is enveloped by loaded names and phrases; ‘Osama Bin Laden’, ‘Al Qaeda’, ‘war on terrorism’, ‘clash of civilisations’ and ‘national security’. And, beneath the shouting and tumult, a worldwide surveillance network was constructed; invasive, all-seeing and anti-democratic to the core.
Under the Bush and Obama Presidencies, the CIA, FBI, and National Security Agency were empowered to intercept and data-mine interpersonal communication and private records. Constitutional protections for individual rights were circumvented. Intelligence oversight committees on Capitol Hill were staffed by proponents of the surveillance state. Furthermore, when social media arrived, intelligence and security agencies in the United States and United Kingdom did not have to rely on professional spies to elicit information. People gave it to them free of charge through their routine use of iPads, iPhones, Google, Facebook and Youtube. These surveillance operations quickly became global in scope. Anglo-American surveillance and security agencies could spy on the entire planet, without restriction and regardless of the stated rationale. Some of these developments were exposed by hacktavists, whistleblowers, journalists and other dissenters. Julian Assange, Bradley Manning, Seymour Hersh, Nick Davies and Laura Poitras became public figures and ‘persons of interest’ to spying agencies. But the roof was really blown off by Edward Snowden; an NSA systems contractor who became, arguably, the biggest whistleblower in history.
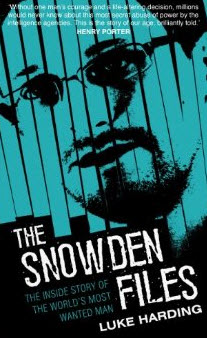
His story is compellingly told in Luke Harding’s The Snowden Files: the inside story of the world’s most wanted man. Glen Greenwald, who was based in Brazil, starts to receive emails from an unnamed source. Documents detailing the methods of US intelligence agencies are on offer. Greenwald is instructed on how to install encryption software on his computer. Similar emails are sent to documentary maker Laura Poitras. After initial NSA documents were sent and decoded, a clandestine rendezvous was arranged. Glen Greenwald, Laura Poitras, and senior Guardian journalist Ewen MacAskill met Snowden in the Mira Hotel, Hong Kong on Tuesday 4 June 2013. The rest, one might say, is history.
Snowden went public in a 17 minute interview filmed and edited by Poitras. Extra-top secret NSA files, hundreds of them, were disseminated to trusted journalists in different countries. Snowden fled from Hong Kong to Moscow as US authorities revoked his passport. With nowhere to go beyond the Moscow airport transit lounge, Putin eventually granted temporary asylum. Snowden became holed up in an unnamed location, presumably in or near Moscow. In the meantime, his video interview and a batch of NSA document slides went viral. A team of Guardian journalists sifted and translated a trove of intelligence material for public consumption. Senior intelligence officers in the United States and the United Kingdom were alerted in advance. This was a very shrewd move, you can imagine the panic. How much do these bastards have? How many copies of each document are out there? Who has them? Suddenly, a power shift occurred. With each new Snowden leak, the CIA, the NSA, the White House, MI5, MI6 and the GCHQ (Government Communication Headquarters) were in damage control mode.
Snowden’s actual revelations about the nature and scope of official surveillance have been extraordinary. I cannot provide a full overview here, a few brief snippets will reveal the gravity of the situation.
- An operational framework called PRISM allows the NSA to obtain collected information from the servers of Microsoft, Yahoo, Google, AOL, Skype, YouTube, Apple and Pal-talk. Some of this information was supplied willingly, other information was secretly extracted from social media companies by the NSA.
- An NSA programme called X-Keyscore allows unauthorised analysts/hackers to search through vast databases containing emails, online chats, and browsing histories.
- Under the acronym TEMPORA, the NSA and GCHG have obtained access to the entire internet backbone via fibre optic cables.
- NSA analysts/hackers have destroyed all known encryption protocols that safeguard internet users’ privacy. They have even managed to slice through the much lauded Tor Network, a specialised web browser designed to hide one’s identity online (a crucial resource for officially targeted activists and journalists).
- Communications information obtained by the NSA is archived for up to one year and stitched into lifestyle pattern profiles assigned to everyone who falls under the agency’s gaze. Information stored in these profiles includes all your phone calls, text messages, emails and other electronic communications including your mobile phone’s location data. An added layer of analysis software on top of this mega database enables analysts to track anybody, anywhere in real time.
- The NSA and GCHQ have routinely targeted journalists, activists, and human rights groups across more than 60 countries. Targets have included Al Jazeera’s internal network, the leadership of UNICEF, and the UN Institute for Disarmament research
- The NSA has also spied upon diplomats and heads of states. The leaders of least 35 nations have been targeted including German Prime Minster Angela Merkel. The information gathered on foreign diplomats and national leaders is used to bend international diplomacy to America’s will.
What are we to make of these revelations? Well, first, every technological function of communication is also a function of surveillance. In this context Harding describes the moment in Hong Kong when Ewen MacAskill took out his iPhone and asked Snowden whether it was ok to tape the interview and take some photos. Apparently, “Snowden flung up his arms in alarm… as if prodded by an electric stick…”. He explained that the spy agency was capable of turning a mobile phone into a microphone and tracking device; bringing it into the room was an elementary mistake in operational security. Second, the targets of spying and surveillance advance beyond obvious enemies. Neutrals, allies and even friends come under the electronic gaze. The NSA spies on the German and French governments, just as the Australian Abbott administration spies on the Indonesians (as part of the ‘Five Eyes’ arrangement). Third, spying is a psychological addiction and a creeping bureaucratic disease. The very processes of communications interception, data-mining and personal profiling take on lives of their own. As in the East German Stasi regime, anybody can be targeted at any time without any apparent reason, a culture of suspicion prevails. Fourth, social justice activists worldwide are the primary targets of official electronic surveillance. Thus, the Snowden revelations should be seen as evidence that the ‘one percent’ who rule the planet will do almost anything to undermine challenges to their power. Fifth, the sheer volume of secret, top secret, and extra-top secret information is impossible to quarantine securely. There will always be a strategically placed whistleblower with qualms of conscience and a conviction that his/her superiors are not performing ethically.
Snowden is a first generation internet whistleblower. His disclosures will encourage and even inspire future whistleblowing activity. This is the real fear of the intelligence operatives who dominate our lives. Sometime, somewhere in the heart of the surveillance state, somebody will, once again, blow the roof off.



But… but… if you have nothing to hide then you have nothing to fear!
Because our government has our best interests at heart, and government agencies and employees never make mistakes, and our governments never push their own agenda ahead of ensuring the safety and rights of all citizens…
oh wait….
Oh please! Are you really that naive. If you have nothing to hide then I guess you wouldn’t be worried if you discovered a stranger living in your attic. Doing no harm just sleeping there and listening to all your private moments??? It can be used also to give those in power a huge advantage over those who oppose them in elections. How about plain old “everyone has a right to privacy”. I guess your attitude is what happens when a countries education system degenerates to the point where people have a very shallow understanding of really important issues.
“Avenging Angel” I can understand your anger if “Lara” was serious, however, I would guess she/he was being sarcastic.
oops! I owe you an apology, it seems I’m losing my sense of humour with age. So sorry.
[…] Blowing the roof off: a review of Luke Harding’s The Snowden Files By Wayne Hope – See more at: https://thedailyblog.co.nz/2014/03/03/blowing-the-roof-off-a-review-of-luke-hardings-the-snowden-file… […]
Comments are closed.