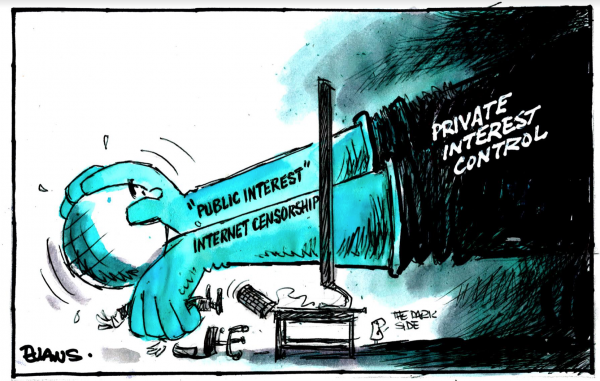
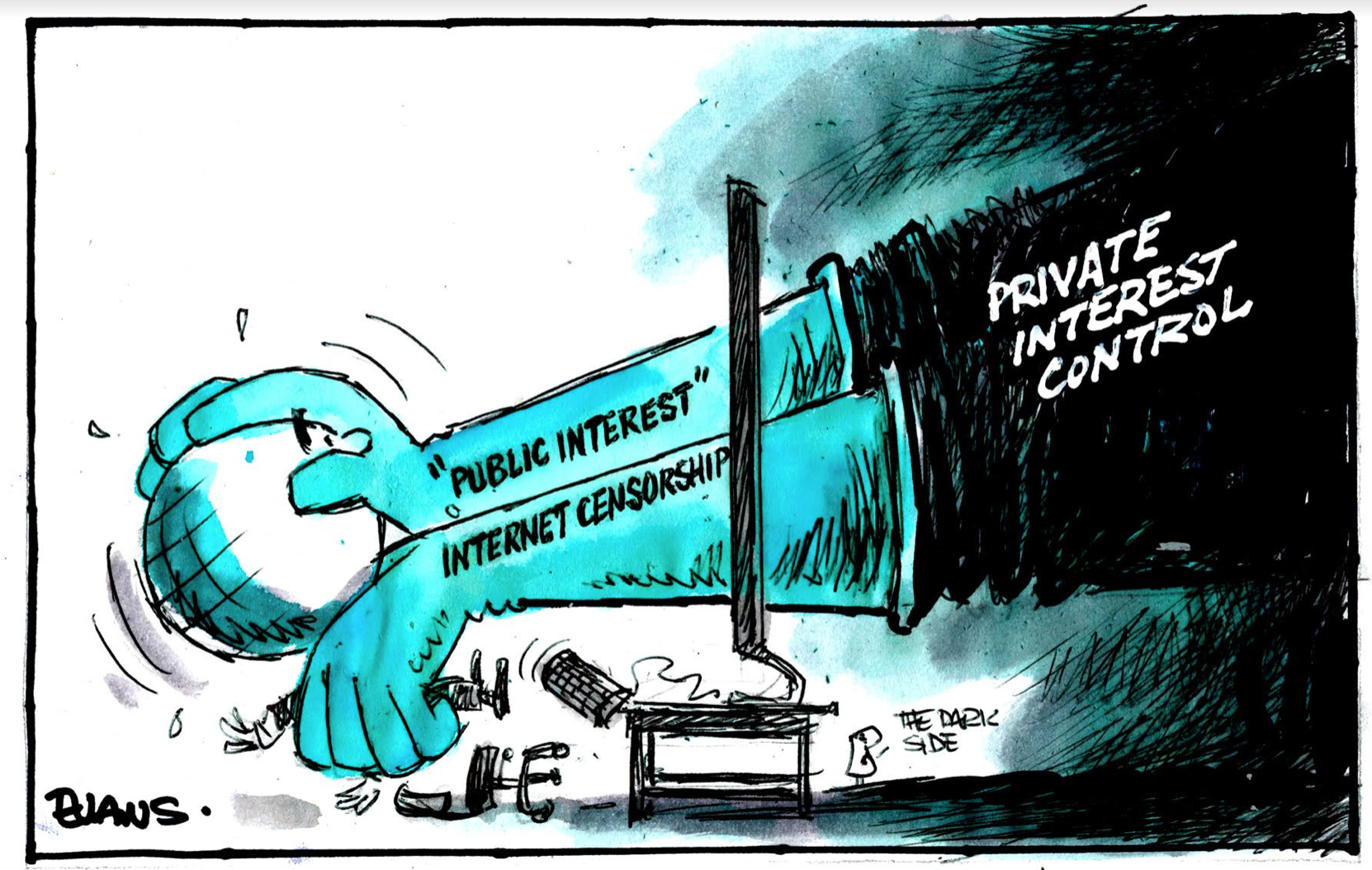
The fact Government Ministers returned from their 5 Eyes spy orgy and faced minimum scrutiny over their plans to force access to encryption shows just how much spin the NZ spy apparatus has spent on numbing the NZ publics attention to the power of the Deep State.
Cue the marketing campaign.
Serious cyber attacks surge, GCSB figures show
Rare speech by GCSB head torpedoed by protesters
More seek shelter from cyber attacks
Cyber-attack targets on govt officials, telco company revealed by GCSB
That’s right folks, the GCSB isn’t a stooge for America and doesn’t feed all it’s info directly to the NSA for their own purposes, it’s really a giant cuddly anti-virus system that keeps your computer safe.

Despite the racism inside the GCSB and SIS, despite the unchecked mass surveillance laws that protect these agencies and the toothless watch dogs set to pretend there is oversight, despite the threat to our democracy, NZers have been conned into believing these Deep State organisations (who have the power to infiltrate and manipulate every single piece of electronic communication you use) are there for our safety and not their power.
NZ was given an Eye of Mordor and in a country as tiny as we are with the lack of real checks and balances against power that power will corrupt.
Allowing them to access encryption is simply more concentration of that power.
The lack of uproar from a numbed and anathematised electorate is the most terrifying part of this.





Big Brother is always watching to make sure they swallow the group-think doublespeak, the fact that Isis and Al-Qaeda work for the same crew hasn’t penetrated the mind smog of the Hairy footed Hobbit mentality nor has the fact they’re here to spy on you not terrorists. Oh Why have the Nine rode forth in the shire oh ancient wise one, because they want your freedom and assets little hobbit, you shall be the hairy foot sandwich’s in the great deli of capitalism, its your “Ring” they shall wear upon the twisted and malformed hands of Mordor, poke out that 5th eye little hobbit, bulldoze those sat links into the sea, grasp freedom with your little outstretched hands and keep that ring intact.
sweet post rickoshay
Very good video of scary OZ laws for 5 eyes.
https://www.youtube.com/watch?time_continue=2&v=eW-OMR-iWOE
+100 Great Post
Orwellian BIG Brother invasion of privacy and undermining of democracy and human rights:
More background to the violation of privacy and human rights issue …Binney ( formerly NSA) is suing the USA government for multiple violations of human rights and the American Constitution
‘William Binney & Arjen Kamphuis – The Dangers of Success – Cambridge University 12-10-2017’
https://www.youtube.com/watch?v=Q-qgmRnqces
Arjen Kamphuis
Published on Oct 22, 2017
“I had the great honor to guest-lecture at Cambridge with Bill Binney for the math faculty. We spoke about mass-surveillance, why it does not work, alternatives and the IT-policy implications of the revelations by whistleblowers such as Bill Binney, Thomas Drake and Edward “Snowden.
….and ;
‘Defend yourself in this digital world – Arjen Kamphuis – TEDxDelft 2018’
https://www.youtube.com/watch?v=mVVlCozNcCw
…and now;
‘Julian Assange’s associate cyber security expert mysteriously missing in Norway’
https://www.youtube.com/watch?v=ovMrYKBRRVo
“Police in Norway are looking into the disappearance of Arjen Kamphuis, a Dutch citizen with links to WikiLeaks founder Julian Assange. Versions on Twitter have ranged from a hiking incident, to a secret assignment, to a CIA hit.”
maybe its time to move forward on this issue and use pictures of our current Ministers…like Andrew Little who is selling us the good work done by the 5 eyes, and has ‘seen the official report into Russian interference into the US election.’. I wonder which report that was? This one maybe??
https://therealnews.com/stories/what-does-the-intercepts-nsa-leak-say-about-russian-vote-hacking
In an interview on REALITY WINNER sentence to 63 months in prison for disclosing a top-secret NSA document describing a hacking campaign directed by the Russian military against U.S. voting systems.
Mehdi Hasan…” Right. So I, I would agree that the intent was a public service. She obviously had this document that she thought which showed that the Russians are meddling in U.S. voting systems, and she wanted to alert the public. Especially a website like the Intercept, which has been associated with challenging that through the writings of Glenn Greenwald. But when you say the document shows the NSA has evidence- let’s go through the document, because I don’t think it shows that. And this is where I think Intercept did not fully explain to readers what the document actually said. And the reason why I think this is important. It’s because this document is the only actual public evidence we have so far that attributes voting hacking attempts to the Russian government. And it’s been the basis for a lot of fear about that alleged Russian hacking since.
So if you look at the document, there’s a legend- and I want to explain it to viewers. And you can see this, Jim, because you’re on the phone with us. But for viewers for watching, we’re going to put it up. So there is a legend. And there are different color codes. So there is a gray line for contextual information. A yellow line for analyst judgment, and a green line for confirmed information. And when you look at the actual attribution on the document in terms of its basis for achieving this to the Russian government, the Russian government attribution does not get a green line for confirmed information. It first gets a yellow line, saying it’s probably within the GRU. But that’s an analyst judgment of that fact that it’s probably within the GRU. It’s not confirmed information. And then furthermore, then there’s a gray line for contextual information, linking the cyber actor that this analyst judgment says is probably within the GRU. Then the gray line links the GRU to this actor that the allegedly carried out the spearphishing attempts.
So if anything, the document itself shows that the NSA, at least according to this document, is not even sure, does not have confirmed information it’s the GRU. It’s simply the judgment of one analyst. And I’m wondering if based on that you are open the possibility that the significance of this document has been inflated.”
incisive, clinical, astute Siobahn is state of the art, what a beauty she is. nothing is hidden from her sight
https://www.bitchute.com/video/EJBLyaqZ1NeR/
Here is the real story behind russia gate, all a cover for a rip of of Russian state by deep state actor behind the Magnitsky act, wonder if he has a bolt hole here>?
+100…yes I can thoroughly recommend this …a real eye opener
The problem is, encrypted communications are such an obscure thing for most people, and so far from the everyday concerns about paying the rent, keep dinner on the table, keeping the shop open, or whatever. There’s a risk people will only understand why this matters too late, and start trying to close the door after the horse has bolted. I just smashed out a blog piece that offers a simple way to explain it, with links to more information:
https://www.coactivate.org/projects/disintermedia/blog/2018/09/07/privacy-is-not-terrorism-but-governments-violating-privacy-is-despotism/
I also recommend anyone who hasn’t seen it already check out the documentary ‘Nothing to Hide’:
https://vimeo.com/189016018
A geek friend and i had been discussing in the past couple of days, a very sloppy piece of internet banking procedure. On reading this blog post i forwarded it to him, this was his reply.
Me starts to wonder if there’s a tie-in with the banking thing we’ve been looking at the last few days.
Once gubbermint has access to encryption, encryption is broken. Once encryption is broken, all international commerce ends. If you cannot protect the transactions, you cannot trade. If you cannot trade….
If “back doors” to encryption must exist by gubbermint edict, then one of two things will happen. One is it will be leaked by someone in the gubbermint. Lets face it, those backdoor keys are literally worth millions to all sorts of hackers, “other gubbermints” (not necessarily friendly), mob/mafia, hundreds of large corporations – just about anyone would want a copy of the backdoor keys. People in government will be bribed and threatened, and someone will crack. Might be the offer of getting a few million in the bank. Might be the offer of getting their kids back, or NOT getting their wife back…
But even if every one in government (not just ours, every foreign government will want their fair copy!) stays true and no one buckles to whatever pressures, there is another issue.
The hackers will know that the keys exist. The value of finding those keys? Just about all hacking assets around the world will be turned to that job. Bitcoin mining rigs – special machines dealing in rather large encryption problems (for that is basically what ‘bitcoin mining” is!) will be re-purposed for that job.
And it won’t take long. The black hats will have the keys within a month tops. Might be 6 months before the public knows the system was cracked, but it won’t be any more.
But the big problem will be the banks. Either financial transactions will be exempt (which means you hide your encrypted messages as financial transactions), or financial transactions will end. Once the systems that protect them cannot be trusted……
And now I’m wondering if there’s a deeper reason for why we’re seeing something that encourages people to give their information out to others.
Comments are closed.